The following is an overview of the events in the Windows Event Viewer generated by the Remote Desktop session host that are relevant to the public key infrastructure.
Event Sources
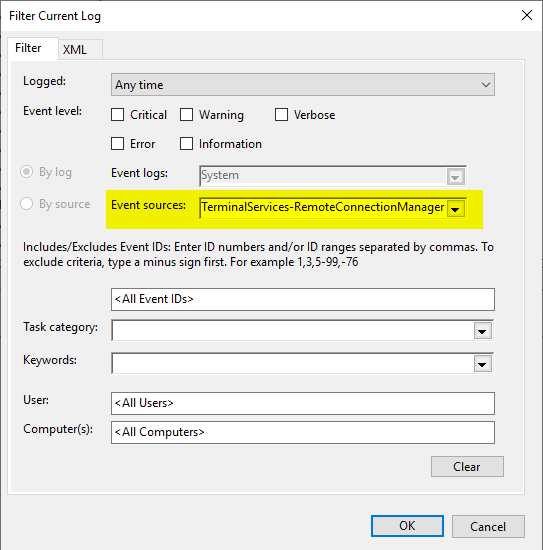
Remote desktop session host events are written to the system log. The following sources contain PKI-relevant events:
- Microsoft-Windows-TerminalServices-RemoteConnectionManager
It is recommended to apply a filter to the system event log.
Do you know TameMyCerts? TameMyCerts is an add-on for the Microsoft certification authority (Active Directory Certificate Services). It extends the function of the certification authority and enables the Application of regulationsto realize the secure automation of certificate issuance. TameMyCerts is unique in the Microsoft ecosystem, has already proven itself in countless companies around the world and is available under a free license. It can downloaded via GitHub and can be used free of charge. Professional maintenance is also offered.
Event source Microsoft-Windows-TerminalServices-RemoteConnectionManager
Do you know TameMyCerts? TameMyCerts is an add-on for the Microsoft certification authority (Active Directory Certificate Services). It extends the function of the certification authority and enables the Application of regulationsto realize the secure automation of certificate issuance. TameMyCerts is unique in the Microsoft ecosystem, has already proven itself in countless companies around the world and is available under a free license. It can downloaded via GitHub and can be used free of charge. Professional maintenance is also offered.
| ID | Type | Event text |
|---|---|---|
| 1051 | The RD Session Host Server is configured to use SSL with user selected certificate, however, no usable certificate was found on the server. The default certificate will be used for RD Session Host Server authentication from now on. Please check the security settings by using the Remote Desktop Session Host Configuration tool in the Administrative Tools folder. | |
| 1052 | The RD Session Host Server is configured to use a certificate that will expire in %2 days. %1 The SHA1 hash of the certificate is in the event data. Please check the security settings by using the Remote Desktop Session Host Configuration tool in the Administrative Tools folder. | |
| 1053 | The RD Session Host Server is configured to use a certificate that is expired. %1 The SHA1 hash of the certificate is in the event data. The default certificate will be used for RD Session Host Server authentication from now on. Please check the security settings by using the Remote Desktop Session Host Configuration tool in the Administrative Tools folder. | |
| 1054 | The RD Session Host Server is configured to use a certificate that does not contain an Extended Key Usage attribute of Server Authentication. %1 The SHA1 hash of the certificate is in the event data. The default certificate will be used for RD Session Host Server authentication from now on. Please check the security settings by using the Remote Desktop Session Host Configuration tool in the Administrative Tools folder. | |
| 1055 | The RD Session Host Server is configured to use a certificate but is unable to access the private key associated with this certificate. %1 The SHA1 hash of the certificate is in the event data. The default certificate will be used for RD Session Host Server authentication from now on. Please check the security settings by using the Remote Desktop Session Host Configuration tool in the Administrative Tools folder. | |
| 1056 | Information | A new self signed certificate to be used for RD Session Host Server authentication on SSL connections was generated. The name on this certificate is %1. The SHA1 hash of the certificate is in the event data. |
| 1057 | The RD Session Host Server has failed to create a new self signed certificate to be used for RD Session Host Server authentication on SSL connections. The relevant status code was %1. | |
| 1058 | The RD Session Host Server has failed to replace the expired self signed certificate used for RD Session Host Server authentication on SSL connections. The relevant status code was %1. | |
| 1059 | The RD Session Host Server authentication certificate configuration data was invalid and the service reset it. If the computer was configured to use a specific certificate, please verify it is available in the certificate store and use the administrative tools to select it again. | |
| 1062 | The RD Session Host server is configured to use a template-based certificate for Transport Layer Security (TLS) 1.0\Secure Sockets Layer (SSL) authentication and encryption, but the subject name on the certificate is invalid. %1 The SHA1 hash of the certificate is in the event data. Therefore, the default certificate will be used by the RD Session Host server for authentication. To resolve this issue, make sure that template used to create this certificate is configured to use DNS name as subject name . | |
| 1063 | Information | A new template-based certificate to be used by the RD Session Host server for Transport Layer Security (TLS) 1.0\Secure Sockets Layer (SSL) authentication and encryption has been installed. The name for this certificate is %1. The SHA1 hash of the certificate is provided in the event data. |
| 1064 | Error | The RD Session Host server cannot install a new template-based certificate to be used for Transport Layer Security (TLS) 1.0\Secure Sockets Layer (SSL) authentication and encryption. The following error occured: %1. |
| 1065 | The template-based certificate that is being used by the RD Session Host server for Transport Layer Security (TLS) 1.0\Secure Sockets Layer (SSL) authentication and encryption has expired and cannot be replaced by the RD Session Host server. The following error occurred: %1. | |
| 1072 | The cn column for the template-based certificate %1 returned an unknown data type %2. | |
| 1073 | The msPKI-Cert-Template-OID column for the template-based certificate %1 returned an unknown data type %2. |